Maritime Security Threats
Current threats to maritime security and shipping from belligerent external forces can come in the following categories:
You might also be interested in BMP5
Piracy
Piracy is just one form of maritime criminality. Read much more about the different types pirate activity here.
Pirates operate in Pirate Action Groups (PAG) who operate several different boat configurations, typically using small high speed (up to 25 knots) open boats or skiffs. PAG boat configurations include:
- Skiffs only.
- Open whalers carrying significant quantities of fuel and often towing one or more attack skiffs.
- Motherships, which include merchant ships and fishing vessels but, more commonly, dhows. Where motherships are used the crew are often held onboard as hostages. Motherships are used to carry pirates, stores, fuel and attack skiffs to enable pirates to operate over a much larger area and are significantly less affected by the weather. Attack skiffs are often towed behind motherships. Where the size of the mothership allows, skiffs may be carried onboard and camouflaged.
Pirate Weaponry
Small arms fire (SAF) and Rocket Propelled Grenades (RPGs).
Pirates may use SAF and RPGs to intimidate Masters of ships to reduce speed or stop to allow them to board. The bridge and accommodation tend to be the main targets for these weapons. Pirates use long lightweight ladders, knotted climbing ropes or long hooked poles to climb up the side of the ship. Once onboard they will make their way to the bridge to try to take control of the ship. When on the bridge they will demand the ship slows/stops to enable other pirates to board. Attacks can take place at any time – day or night – however experience shows attacks at dawn and dusk are more likely.

Intent
The intent of pirates varies according to several enabling factors ; Somali pirates generally intend to hijack the ship and hold the crew for ransom. The usual practice is to keep the crew onboard as negotiations progress, keeping both the crew and the ship together. Seafarers have occasionally been separated by nationality and taken ashore. It is in the interests of the pirates to keep their captives alive, although cases of intimidation and torture have occurred. West African piracy has followed a different pattern.
Anti-Ship Missiles
Long range, accurate and powerful weapons and have been used against military ships.
- Their use against merchant ships associated with regional conflict cannot be discounted.
- Other ships may be hit if the missile controller targets the wrong ship or the missile homes in on an unintended target.
Remember:
- Stay informed about geo-political tensions
- React to heightened tensions
Mines

Sea mines have been used to deter and deny access to key ports.
These mines are usually tethered or anchored but may break free from moorings and drift into shipping lanes. Transiting merchant ships are not usually the target and it is recommended ships use the established routes such as the MSTC when passing through the identified areas.
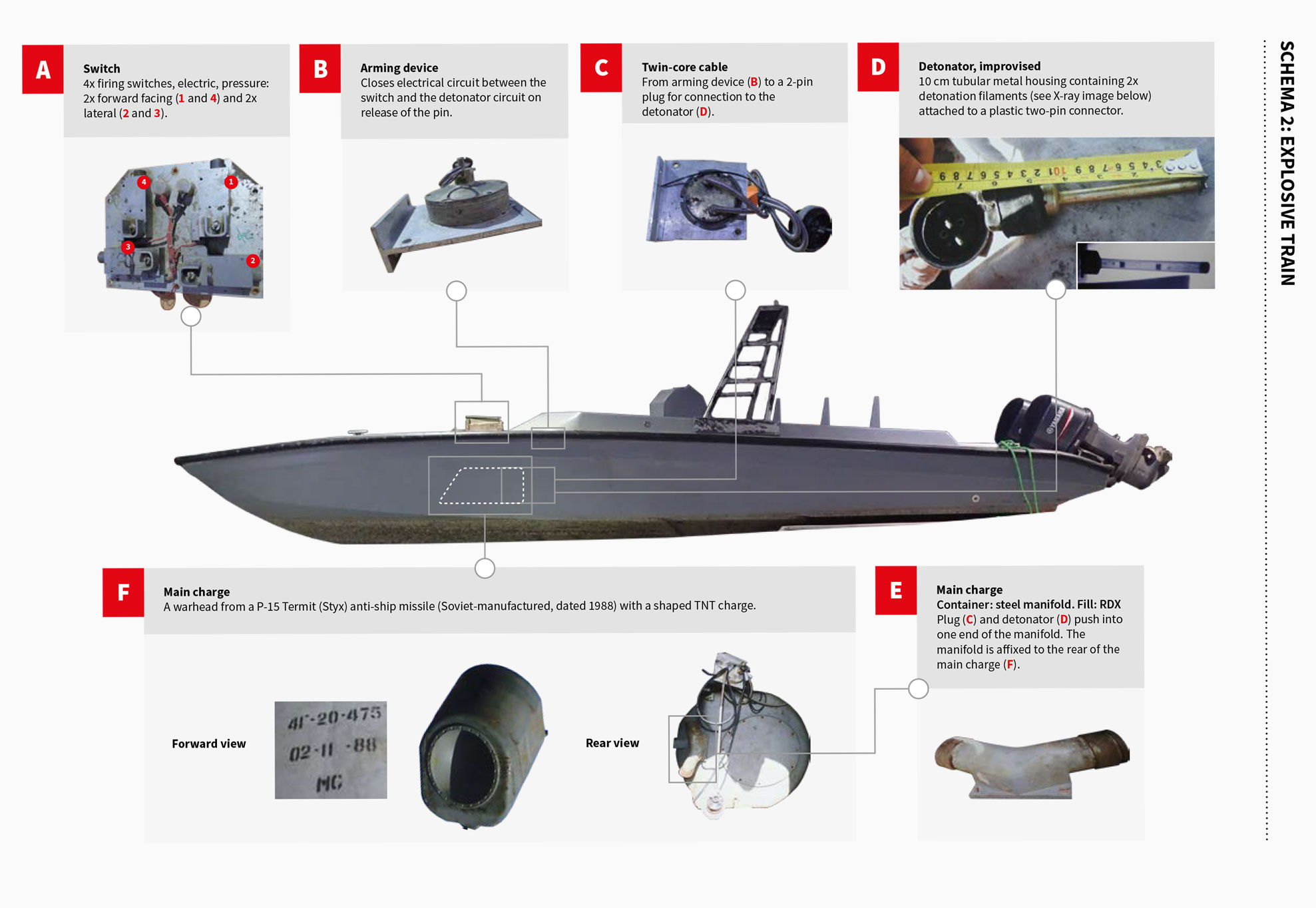
Water Borne IED (WBIED)
WBIED attacks have been used against warships and merchant ships in the southern Red Sea/BAM/western area of the Gulf of Aden.
- Incidents have highlighted attacks by different groups operating in the region:
- WBIED used in regional conflicts have been aimed at harming those associated with the conflict. These boats have been unmanned and operated remotely.
- WBIED used by extremists on manned vessels have been aimed at merchant ships.
- An attack involving a WBIED is likely to involve one or more speed boats operated by a number of individuals approaching and firing both small arms and RPGs. Masters should recognise the intent of these attacks is to cause damage and not necessarily to board the ship. Mitigation measures to prevent the speed boat making contact with the ship’s hull are limited.
Maritime Security Geographical Regions
Where are the current hotspots that warrant the application of BMP5?
Threat and Risk Assessment
What is a security risk assessment? The threat assessment must include all regional security threats.

Voyage Planning
The output of the risk assessment will help develop the ship's voyage plan.
Ship Protection Measures
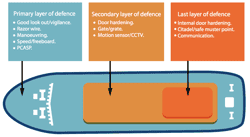
BMP5 provides Ship Protection Measures (SPM) based on real-life experience of piracy attack and incidents of maritime crime.

Reporting Guidelines
All ships are strongly encouraged to inform military organisations of their movement